🚨 DNA doesn’t belong to a stranger: The Nancy Guthrie mystery takes a new turn as all suspicion points to inside the house.
The masked figure, the black gloves, and the momentary “disappearance” from the data are redrawing the entire timeline. As new evidence rules out the possibility of a random abduction, the biggest question remaining is: who was really behind that door that night?
Neighbors described the area as quiet, residential, and low crime—a place where the unexpected rarely happens. But in the early hours of February 1st, 2026, everything changed.
II. The First Signs
At 2:28 a.m., something inside Nancy’s home went silent. Not a scream, not an alarm—her heart monitor. Minutes earlier, a figure dressed in black stood outside her front door, studying the camera as if he knew exactly where to look. The footage, captured by her doorbell camera, cut abruptly. Law enforcement later confirmed the camera housing showed signs of force. The FBI released the footage publicly, showing a masked suspect at Nancy’s doorstep without a backpack. Investigators believe this image was taken before the morning of her disappearance.
III. The Timeline Shifts
For weeks, the focus remained on what happened outside Nancy’s home—the masked figure, the disabled camera, the narrow window between recorded movement and the moment her medical device stopped transmitting. But according to new investigative updates, law enforcement sources confirm the timeline is no longer centered on the front door. It begins inside the house.
Digital forensic reviews of Nancy’s phone and home systems suggest interior activity before the exterior camera was disrupted. Authorities have not released full details, but they confirm the timeline inside the home is being reassessed. If entry occurred earlier than originally believed, the event was not spontaneous—it was planned.
IV. Evidence and Scrutiny
The FBI has confirmed that DNA collected from the property does not match Nancy Guthrie or any immediate family member. The DNA was entered into CODIS, the national combined DNA index system. There were no matches. When a DNA profile does not return a result in CODIS, it typically means the person has never been convicted of a qualifying offense, or the sample belongs to someone not yet identified in the database.
Investigators have since expanded their forensic approach beyond CODIS. Law enforcement officials have confirmed they are reviewing additional biological evidence collected both inside and outside the residence, including trace material recovered during secondary searches. This is not routine. When investigators return to a property after the initial processing, it usually indicates either new information has surfaced or earlier findings require closer review.
Detectives re-entered Nancy’s home days after the initial search. Evidence markers were repositioned. Items were re-examined. Digital devices were reviewed again. The reason, according to officials, is that something did not align. At the center of this shift is the 16-minute gap between the final exterior footage and the medical device disconnect.
V. A Narrowing Window
For weeks, that window defined the case. Now, investigators believe the activity may have begun before that clock started. If true, that suggests familiarity with the property, and that is where attention has narrowed. Authorities have repeatedly stated that no official suspect has been named. Sheriff Chris Nanos of the Pima County Sheriff’s Department has emphasized that investigators are examining all possibilities. The FBI has echoed that position.
However, multiple searches of a specific residence have been confirmed. Annie Guthrie, Nancy’s daughter, and Annie’s husband, Tomaso Hayion, live approximately four miles from Nancy’s home. Public records confirm that investigators conducted two searches at their residence—one consensual and one under warrant. Law enforcement has not disclosed what prompted the second search or what was collected. But here is the key point: a second warrant requires judicial approval based on probable cause. It signals that investigators believe additional evidence may be located at that address. That does not mean guilt. It means scrutiny.
Tomaso Hayion was the last documented person to see Nancy alive. He drove her home after dinner. That fact has been confirmed by both family members and investigators. In high-profile disappearances, the last person to see the victim often receives immediate attention. That is standard investigative protocol. What makes this development different is timing. Sources close to the investigation indicate that law enforcement focused on specific movements in the hours after Nancy was dropped off.
VI. Data and Digital Reconstruction
Modern investigations rely heavily on data. Door sensors, phone pings, vehicle systems, home networks. Even in cases where surveillance footage is limited, metadata often tells a more precise story than eyewitness accounts.
According to officials, multiple data points from the night Nancy disappeared are being synchronized to create a minute-by-minute reconstruction. That process is ongoing, and it has produced what investigators describe as a person of interest. Authorities have not publicly named that individual. However, they confirm that investigative focus has narrowed.
When asked whether family members have been cleared, Sheriff Nanos stated that no one has been fully eliminated from consideration. That statement is important. It means the investigation remains active and fluid. It also means speculation must be handled carefully.

VII. The Role of Media and Public Pressure
Nancy Guthrie is the mother of Savannah Guthrie, co-anchor of NBC’s Today Show. Media coverage accelerates quickly. Rumors spread. Online commentary grows louder. But investigators move at a different pace. They build cases through corroboration. And corroboration takes time.
The FBI has confirmed receiving more than 30,000 tips. That volume creates both opportunity and distraction. Each tip must be reviewed, logged, and evaluated. At the same time, forensic labs continue processing material. The reward for information leading to Nancy’s recovery now stands at $100,000—$50,000 from the FBI and $50,000 from the family. Reward increases typically occur when investigators believe public cooperation may produce actionable leads.
Authorities have also confirmed reviewing surveillance footage from surrounding neighborhoods within a five-mile radius. That includes footage from private residences and businesses. One particular clip recorded at a property miles away from Nancy’s home shows a person carrying a backpack similar in design to the one worn by the masked figure at Nancy’s door. Investigators have not confirmed whether that individual is connected, but they are examining the timing. The timing is everything.
VIII. The Shift in Narrative
For weeks, the case centered on a masked stranger. Now, investigators are evaluating whether the suspect was someone with knowledge of the home’s layout and Nancy’s routine. That distinction changes public perception. Because random attacks are unpredictable, targeted events are traceable. The difference lies in planning.
As of this recording, no arrests have been made, no formal charges have been filed, but law enforcement confirms that new evidence has tightened the circle. And that is why this case is no longer just about disappearance—it is about identification.
IX. Behind the Scenes: The Investigative Process
By the second week of the investigation, law enforcement shifted resources toward one central objective: reconstructing movement through data, not theory, not rumor. Data. The Pima County Sheriff’s Department confirmed that multiple forms of digital evidence were under review. That includes cellular records, home network logs, vehicle system data, and geolocation timestamps.
When physical evidence leaves gaps, digital records often fill them. This case is no exception. Investigators began with Nancy’s personal devices. Her phone, tablet, and home Wi-Fi router were collected for forensic imaging. Digital forensics specialists extract complete system copies before analysis that preserves metadata, connection times, login attempts, background processes, and network traffic.
Authorities confirmed that Nancy’s devices showed no outgoing communication after she returned home that night—no calls, no text messages, no emergency attempts. That absence is significant. It suggests either she had no opportunity to use her phone or her phone was not accessible.
Next came cellular mapping. Law enforcement requested tower pings covering a radius around Nancy’s home during the early morning hours. Cell providers retain connection logs that show which devices registered with nearby towers. Investigators are not looking for names at this stage; they look for unknown numbers that appeared briefly and then disappeared. Temporary presence stands out.
According to sources familiar with the case, analysts isolated several devices that connected to towers near Nancy’s property during the window under review. Most were consistent with normal residential traffic. A few were not. Those numbers are now being traced through subscriber records and historical movement patterns. This is standard in targeted abduction cases. Patterns matter more than one-time hits.
X. Vehicle Telematics and Neighborhood Surveillance
Simultaneously, detectives reviewed vehicle telematics. Modern vehicles store more data than most drivers realize: ignition times, door openings, mileage intervals, GPS logs in some models. Even vehicles without subscription navigation often retain event data internally. When investigators execute a warrant on a vehicle, they extract onboard computer information. That process can reveal whether a car moved during specific time frames and whether doors were opened or closed.
The sheriff’s department confirmed that at least one vehicle associated with the case was examined under warrant. They have not publicly released findings. But here is what we know from official statements: the vehicle analysis was requested after new digital correlations surfaced. That timing matters. If a vehicle’s movement aligns with unexplained cellular activity, investigators gain a stronger picture of sequence.
In parallel, neighborhood surveillance canvassing intensified. Deputies knocked on doors within a multi-mile radius. They requested access to private security systems, doorbell cameras, and driveway recorders. In suburban investigations, private footage often outperforms city cameras because residential systems capture sustained motion rather than traffic snapshots. And authorities have confirmed they reviewed hours of footage from homes along potential access routes.
They are not only looking for the masked figure. They are looking for vehicles that appear more than once—repeated drive-bys, slow turns, lights switching off before entry. These patterns build a behavioral profile.
XI. Power Grid Data and Timeline Synthesis
According to statements made during press briefings, investigators also analyzed power grid data. Utility companies maintain records of service fluctuations. If lights were turned on or off abruptly in adjacent homes, that data sometimes correlates with outdoor movement or door activity. It may sound minor. It is not. In cases without witnesses, digital breadcrumbs become the witness.
Detectives brought in specialists trained in digital timeline synthesis. That process merges all available data—phones, routers, vehicle logs, surveillance clips—into a unified timeline. The goal is simple: identify inconsistencies. If one device shows activity at 1:12 a.m., but a corresponding system shows inactivity, that gap demands explanation.
Authorities have not disclosed the specifics of the discrepancies they found. They have confirmed that the timeline reconstruction led them to re-interview individuals connected to Nancy. Re-interviews are strategic. Detectives compare previous statements against newly developed data. They measure accuracy against timestamps.
In high-profile cases, interviews are recorded and preserved. Language matters. Wording matters. Time references matter. Investigators are trained to detect drift—small shifts in narrative over time. That is where psychological depth enters the investigation.
XII. Behavioral Analysis and Entry Points
Meanwhile, the FBI joined local authorities to assist with data analysis. Federal resources expand technological capabilities, especially when dealing with complex digital mapping. The FBI confirmed that behavioral analysts were consulted. A behavioral analysis does not determine guilt. It evaluates likelihood. It studies planning indicators, risk tolerance, and knowledge of the environment.
In cases involving older victims, analysts often examine whether the event appears opportunistic or directed. Directed events show preparation, knowledge of routines, understanding of entry points, awareness of vulnerabilities. Those elements are now central to the review.
Publicly, investigators have stated that there are no confirmed signs of forced entry at the primary access points of the home. That statement is careful. It does not eliminate entry. It suggests access may have occurred through an unsecured route or through familiarity. If access did not require force, it narrows the field.

XIII. Forensic Breakthroughs: The Black Glove
The first major change in this investigation did not come from a press conference—it came from a roadside recovery. On February 12th, investigators located a black glove about two miles from Nancy Guthrie’s residence, in an open area near the side of a road. The FBI later described it as potentially linked to the person seen in the available surveillance imagery.
At first glance, a discarded glove sounds ordinary. But in a missing person case, it can be anything but. A glove is not just clothing; it can be a carrier of trace evidence—fibers, soil, and biological material. It can show wear patterns and help investigators estimate how recently it was left in that location.
The FBI publicly stated that the glove appears to match the gloves worn by the subject seen in the surveillance footage and that it contains DNA evidence. That statement is careful. It does not claim the glove belongs to the person in the footage. It says it appears to match what is visible and it contains a DNA profile. In court, “appears to match” is not proof—it is a lead. And from that lead, the case begins to shift toward new evidence and a suspect direction.
XIV. DNA and the Search for Identity
Once an item is recovered and properly logged, it is transported under chain of custody rules. The lab work begins: visual inspection, documentation, and controlled sampling. DNA extraction focuses on high-contact zones—fingertips, inner palm, wrist seam, outer surface.
If a sample is usable, analysts can create a DNA profile—a coded set of genetic markers that can be compared against other samples. In this case, the FBI indicated that the glove contains DNA evidence and that it appears to match the gloves worn by the person seen in surveillance imagery. The Pima County Sheriff’s Department later said that DNA from a glove did not yield a match and also did not match a separate sample found at Nancy Guthrie’s home.
There can be more than one glove, more than one sample, and more than one profile under analysis at the same time. The DNA from the glove did not match the sample recovered at the residence. Why does the glove still matter? Because investigators are building a matrix of comparisons. If a glove has a profile and the residence has a separate profile, that can mean multiple individuals were involved, or that one of the samples is not connected to the core event. It can also mean contamination, transfer, or unrelated contact at the property.
XV. Genealogy and Next Steps
When a DNA profile is developed, the first major comparison route is CODIS, the national criminal DNA database. If a profile does not match anyone in CODIS, it does not mean the person is unknown—it means they are not in that database. Investigators then expand comparisons against any other profiles collected in the case and consider other legal methods, including commercial genealogical databases.
The Pima County Sheriff’s Department stated that investigators were turning to commercial genealogical databases in the absence of a match. Commercial genealogical searches do not typically identify a person directly—they look for partial matches to relatives who have opted into law enforcement matching. From there, investigators can build family trees and narrow the pool. In a genealogy-led investigation, a suspect may start as a cluster, a family line, a geographic circle, a set of male relatives in a certain age range. Then it narrows one branch at a time.
XVI. The Power of Data
When investigators say they are waiting on DNA results, they may be waiting on extraction confirmation, profile development, quality checks, comparison runs, retesting for verification, legal review for genealogy submission. In this case, local reporting noted that law enforcement was waiting for confirmation of DNA testing connected to gloves recovered near Nancy Guthrie’s home. Waiting does not mean stalled—it means the lab is inside the decision tree.
XVII. Public Appeals and Community Role
When the FBI releases or updates a missing person flyer, every word is chosen carefully. Flyers are built for two goals: public recognition and tip relevance. With the release of surveillance images and videos, the FBI updated the Nancy Guthrie missing person flyer. Flyer updates typically include physical description, clothing details, items carried, direction of travel if known, tip line info. None of that is proof, but it helps someone out there connect a memory to a case—a neighbor who saw someone dressed similarly, a driver who noticed a person walking where they shouldn’t have been, a store employee who remembers a purchase.
That is how cold visual evidence becomes warm human recognition. And recognition leads to a name. That is the “suspect found” moment the public often expects—not a public accusation, but a privately identified lead that investigators can verify through records, interviews, and lawful evidence collection.
XVIII. Managing Rumors and Media
In active cases, rumors spread fast, especially around searches and detentions. When investigators serve a warrant at a residence, anyone inside is technically detained as part of standard procedure so investigators can safely conduct the search. That clarification prevents the public from misreading standard procedure as proof of guilt. A detention during a search is not an arrest—it is control of the scene.
As evidence becomes more technical, especially when genealogy and lab comparisons are involved, agencies often limit public statements. Recent reporting noted that on February 24th, the Pima County Sheriff’s Department said it would limit further updates unless new information warrants release. That is what you do when you are approaching a critical point. You don’t want public chatter to shape witness statements, false confessions, or attention seekers showing up. You don’t want the person responsible to learn what you have. Less talk, more proof.
XIX. The Message and Ransom Note
In early February 2026, authorities confirmed they were evaluating a message connected to Nancy Guthrie’s disappearance. Public reporting described it as a message linked to potential kidnappers. But even in that wording, the uncertainty is built in. Because until law enforcement confirms who sent it and why, it is not evidence of anything—it is only a signal that someone wants to be heard.
Savannah Guthrie, Nancy’s daughter and co-anchor of NBC’s Today Show, released a video plea. The family acknowledged receiving a message and said they were willing to pay for Nancy’s safe return. That kind of statement is not made casually. When families speak publicly in cases like this, it’s usually because they believe there is a real chance the person watching will respond to pressure or because investigators think the public appeal can create a reaction that produces a lead.
But there’s a risk. Once you say “we will pay,” you invite copycats, hoaxers who want money, people who want attention, and people who want to send the investigation in circles. That is why investigators treat every communication like a forensic object. It has to be tested, not believed.
XX. The Role of Cryptocurrency and Technical Analysis
An entertainment outlet reported receiving an alleged ransom note demanding a substantial amount of Bitcoin, claiming the amount was in the millions and providing a specific Bitcoin address. The report said they verified the address exists. But verifying a Bitcoin address exists is not the same as verifying the sender is real. A Bitcoin address can be created in minutes. Anyone can generate one. Investigators don’t stop at “the address exists”—they look at the blockchain, check prior activity, track whether the address was created and posted in connection with other scams, monitor whether funds move through it, and set up controlled pathways so that if money does move, it leaves a trail.
Cryptocurrency demands don’t automatically mean the sender is smart. In many cases, they’re careless. And because cryptocurrency isn’t invisible, every movement becomes a line investigators can follow. A message can look powerful, but it can also expose the sender.
XXI. Communication and Psychological Pressure
When authorities learn of a message tied to a missing person case, there are immediate decisions behind the scenes: Is this message direct or secondhand? Is the sender asking for money or trying to control behavior? Is there proof? Does engaging help or harm? In some cases, investigators advise families not to respond publicly. In other cases, they coordinate a public message that is carefully worded. When families speak without coordination, they can accidentally reveal what investigators know or don’t know. They can also trigger the sender to change tactics.
The sheriff’s posture—cautious optimism, controlled language—is both hope and strategy. It keeps the public engaged, keeps tips coming, avoids locking the investigation into one outcome. If the person responsible is watching, a statement like that can pressure them to communicate again or pressure them into a mistake.
XXII. The Challenge of Deadlines and Consistency
One detail in public reporting around alleged ransom messaging is the idea of deadlines and large demands. Deadlines create urgency for viewers. For investigators, deadlines create problems because deadlines push families to act quickly, and quick action is where mistakes happen, especially if money is involved. Investigators prefer to slow the pace even when a message demands speed. They slow it with controlled responses, verification demands, by forcing the sender to repeat themselves. Because repetition is where cracks appear—a hoaxer can write one convincing message, but it’s harder to maintain a consistent lie over multiple exchanges.
XXIII. Major Platform Coverage and Public Impact
When the missing person is tied to a national TV anchor, the reach is immediate. Millions of people who don’t live anywhere near Tucson suddenly know the name, the face, and the basic outline. That coverage helps—more eyes can mean one good tip—but it also creates a serious side effect. When a case is this visible, false leads become a second wave. Investigators have to protect their tip lines from being overwhelmed by people repeating internet theories, protect the family from scams, protect witnesses from harassment, protect evidence from exposure.
This is why law enforcement messaging becomes tight—not because they don’t care, but because the case becomes fragile under noise.
XXIV. Narrative Control and The Suspect Search
When the public hears “new suspect found,” they imagine a name on a screen. Investigators don’t start with a name—they start with a narrowing. In communication-driven stages of an investigation, narrowing often comes from one of two sources: a communication that includes a detail only the offender could know, or a communication that can be traced technically—a mistake in transmission, a reused account, a logged-in device, a pattern.
At this stage, authorities have not publicly identified the sender of any message as a confirmed offender. Reporting makes clear that even in Savannah Guthrie’s plea, it was not confirmed whether the message was truly from a kidnapper. Accuracy is the difference between a documentary and a rumor mill.
XXV. The Weight of Waiting
A family is not only waiting—they are being tested. Tested by silence, tested by claims, tested by messages that may or may not be real, and tested by the knowledge that every public sentence might cause a reaction. That kind of pressure changes people. It changes how they talk, how they sleep, how they trust. It also changes how investigators work the case because investigators must now manage the human side and the technical side at once.
When a message enters a case, it doesn’t explain anything. It adds another layer—another possible route to the truth or another attempt to hide it.
XXVI. The Call to Action
If you’re watching because you want the clean version of events—verified reporting, clear sourcing, no rumor—this is the moment to pay attention. Because in cases like this, the biggest shifts don’t always happen on camera. They happen when one message turns into two, then three, until the sender slips, or until a real witness decides they can’t stay silent anymore.
Right now, here is what is true and on the record: Public reporting confirms the family acknowledged receiving a message connected to the case and made a public plea, including willingness to pay for Nancy’s safe return. Public reporting confirms an alleged ransom note demanding Bitcoin was sent to a media outlet. But authenticity of any such note is not established simply by its existence. Public reporting confirms ongoing law enforcement work continues under cautious public language, including remarks suggesting hope Nancy may still be alive.
XXVII. Conclusion: The Meaning of the Case
Nancy Guthrie remains missing, but her case is no longer undefined. It is being reconstructed minute by minute. In modern investigations, data rarely lies. The question is not whether the truth exists in the record. The question is who that record is pointing toward.
The investigation is no longer broad—it is methodical. The next phase will determine whether the digital trail supports charges or eliminates key individuals entirely. If you value careful analysis over noise, follow the evidence as it develops and separate fact from speculation.
In most missing person investigations, the public sees a small fraction of what detectives actually do—a few lines in a press release, a photo, a tip number. This case did not follow that pattern. From the first week, Nancy Guthrie’s disappearance became a national headline and the investigation entered a new environment, one where every decision, every sentence, and every silence would be judged in real time.
That pressure came from everywhere at once—national news outlets, social media accounts posting updates with no sourcing, true crime channels chasing speed, and critically, a media dispute that moved attention away from facts and toward accusation.
The next step is not louder coverage—it is quieter proof. And the people doing the work know that the moment they choose a suspect publicly, they need more than suspicion. They need a case that survives the hardest question of all: Can you prove it?
Nancy Guthrie’s story is not just about disappearance—it’s about the relentless search for truth, the resilience of a family, and the patience of an investigation that refuses to be rushed by rumor or noise. As the data points converge, the answer is coming. And when it does, it will be built not on speculation, but on evidence that can stand in court.
News
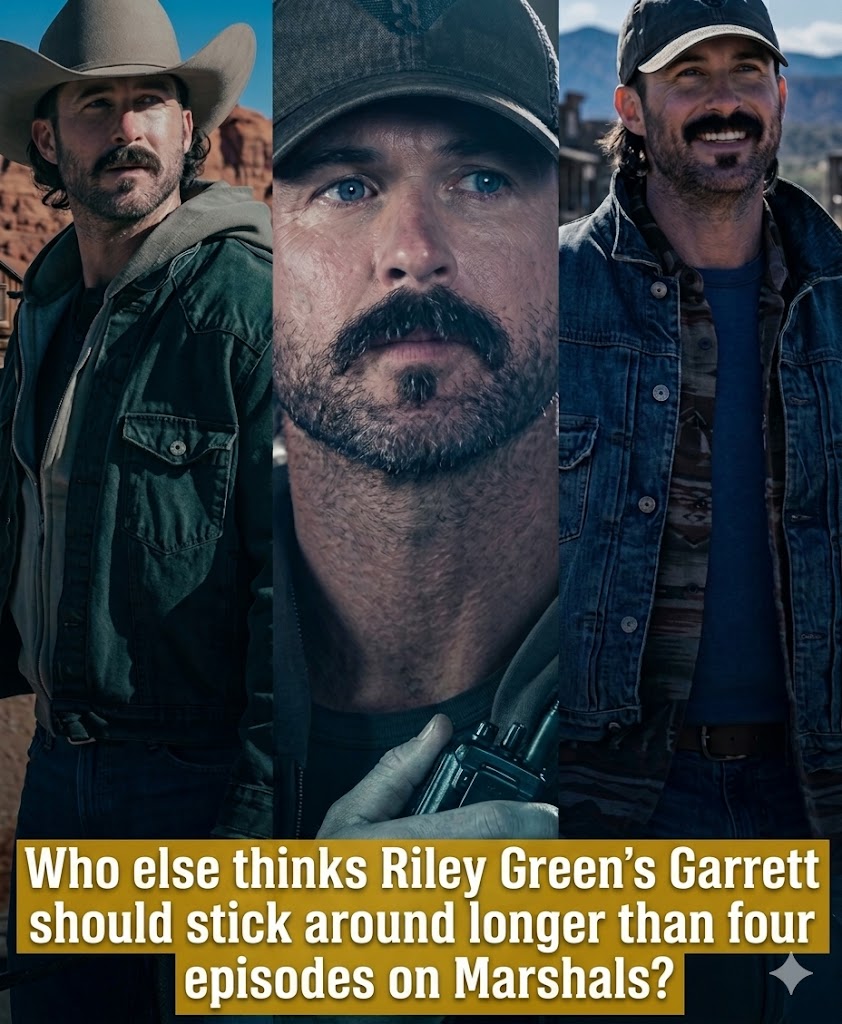
Riley Green Didn’t Feel Like A Guest Star In Marshals — He Felt Like Garrett Had Been There From Day One..
Riley Green’s appearance in *Marshals: A Yellowstone Story* might initially lead many to think of him as a standout guest star—a familiar face brought in for publicity. But after just a few scenes, that feeling quickly dissipates. The character of Garrett doesn’t enter the story as a newcomer. He appears as if he’s always been […]
“Grief is the price we pay for love. And to have loved her that much? That’s a debt I’d sign for every day of my life.” — Felix Long, Marshals Ep. 6…
In *Marshals: A Yellowstone Story*, there are lines of dialogue that exist not just to tell the story, but to “stay”—haunting the viewer like a lingering echo. Felix Long’s line in Episode 6 is one such moment: “Grief is the price we pay for love. And to have loved her that much? That’s a debt […]
If she were alive, Madeleine would turn 23 on May 12th. Despite a book and a Netflix documentary series, her whereabouts remain a mystery….
Nineteen years ago, on a night like this, a three-year-old girl disappeared from a holiday apartment in southern Portugal—the beginning of one of the most sensational disappearances in the modern world. That girl was Madeleine McCann. She disappeared during a family holiday at Praia da Luz on the evening of May 3, 2007. That night, […]
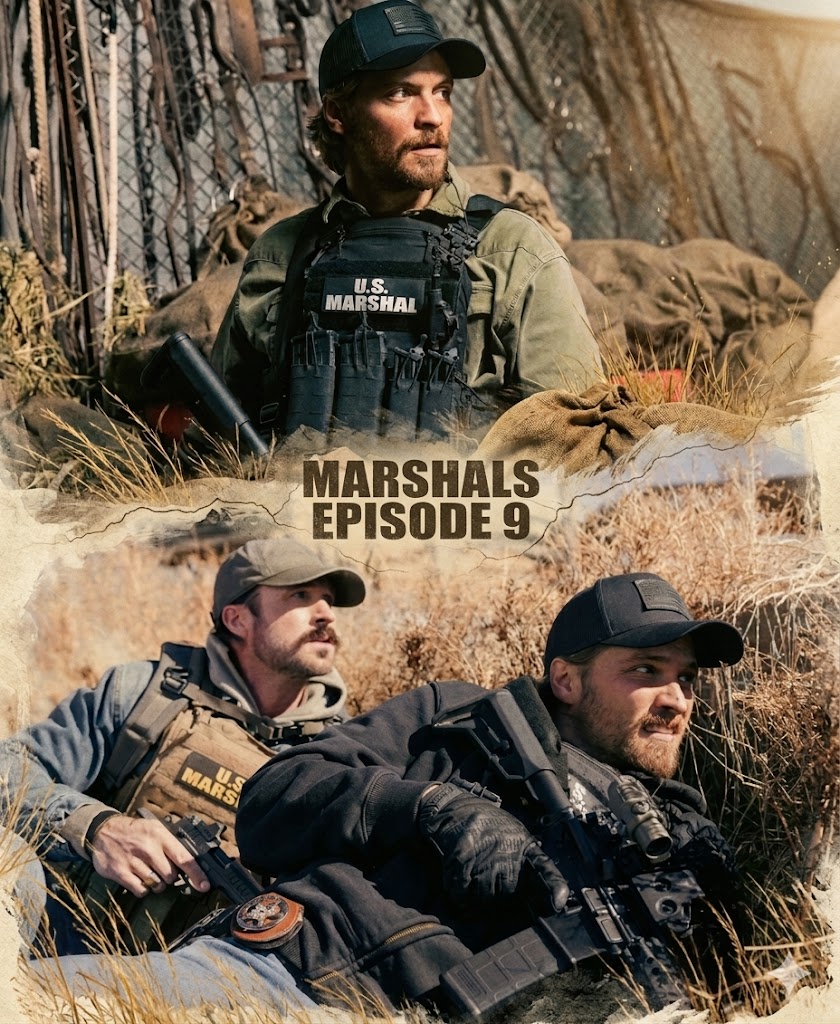
The Ghost Of Rhoner May Be What Finally Breaks Kayce Dutton In Marshals…
Rhoner is not just Kayce Dutton’s past—it’s a wound that never truly heals. His death on a mission in Afghanistan has haunted Kayce, Cal, and Garrett, causing every present decision to be influenced by that past mistake. In Episode 9, when the perilous situation repeats itself, the greatest fear is no longer mission failure… but […]
A PERFORMANCE THAT BECAME TOO REAL…
In a series with such emotional depth as *Outlander*, the line between acting and an actor’s personal experience sometimes becomes so thin that it’s almost indistinguishable. César Domboy’s final scene with Fergus Fraser is a prime example of this phenomenon – where a moment on screen transcends the script, becoming a collective experience for the […]
“Episode 8 Turns Everything Around: Kayce No Longer Hunting… But Becoming the Target?”
🧨 “Episode 8 Turns Everything Around: Kayce No Longer Hunting… But Becoming the Target?” In a series built around action-packed pace and life-or-death choices like *Marshals*, a rescue mission turning into a trap isn’t just a plot twist, but a strategic turning point – where the story shifts from active to passive, from control to […]
End of content
No more pages to load